Macro viruses
A macro virus is defined as “a computer virus written in the same macro language used for software applications, such as word processors.”

A macro virus is defined as “a computer virus written in the same macro language used for software applications, such as word processors.” Microsoft Word and Excel are two examples of applications that feature powerful macro languages, which are embedded in documents so they run automatically when the documents are open. A macro virus subsequently releases a “chain of events in conjunction with the application.”

Help protect your digital life on your devices.
Are you afraid of losing your personal information or all the precious things on your computer? Get comprehensive protection with Norton Security Deluxe across all your devices – up to 5 PCs, Macs, smartphones or tablets.
Create an account today and try it free for 30 days on up to 5 of your devices.
How They Spread
Macro viruses spread whenever a user opens or closes an infected document. The most common methods of spreading such viruses include:
- Email attachments
- CD-ROM
- Internet
As with many other forms of viruses and malware, macro viruses are difficult to detect.
What They Do
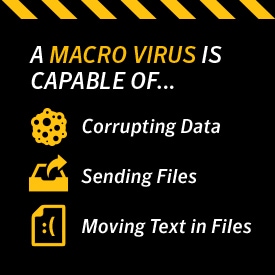
These viruses are programmed to do practically anything with a PC. This means a macro virus is capable of creating new files, corrupting data, moving text, sending files, formatting hard drives, and inserting pictures among other things. One of their more popular uses is as transportation for destructive viruses and malware.
A Classic Example
A now-classic example of a macro virus is the Melissa Virus from 1999. Opening an email containing a document infected with the virus would cause the email to send itself to the first 50 addresses in the user’s contact list. The virus subsequently replicated at an extraordinarily fast rate.
Application Rather Than Operating System
Because a macro virus centers on an application rather than an operating system, it has the ability to infect any operating system, including those on non-Windows computers.
Symptoms of a Macro Virus Infection
Symptoms of a macro virus infection include:
- Your computer runs slower than normal.
- Your computer asks you for a password on a file that normally doesn’t require one.
- Your computer saves documents as “template” files.
- Your computer features strange error messages.
How Do I Get Rid of a Macro Virus?
Getting rid of a macro virus requires taking it to a professional or checking manually for virus signs.
“To check for viruses manually, choose Tools | Macro | Macros and compare the resulting list of macros with the list you created earlier,” M. David Stone wrote for PC Mag in 2001. “Follow this procedure with the Macros in: box set for Normal.dot and for each file in your Startup folder.
“Pay particularly close attention to any macros named AutoExec, AutoOpen, AutoClose, FileExit, FileNew, FileOpen, FileSave, FileSaveAs, and ToolsMacro,” Stone added. “The first three names identify macros that run automatically. The rest replace built-in commands in Word and are common choices for viruses. If you have legitimate macros with these names, look at the contents of each with the aid of the Edit button. If none of your macros have been replaced or modified by a virus, you're almost certainly virus-free.
”How Do I Prevent Macro Viruses From Infecting My Computer?
As with all forms of cyber viruses and malware, prevention is best. Use the following tips to protect your computer:
- Update your security system regularly to guard against new types of viruses.
- Update your computer regularly to ensure optimal protection. For example, if you have Windows 8 and are being prompted to update to Windows 10, do it.
- Use digital signatures. They identify download sources so you can be sure what you’re downloading and running isn’t a risk.
- Download reputable antivirus software if you haven’t already.
Macro viruses are among the sneakier methods of infecting a computer. Stay aware of the latest information on these and all other cyber viruses, and give your computer a thorough scan if it hasn’t had one in awhile. And again, if you’ve been ignoring update notifications, now is the time to take action.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.





Want more?
Follow us for all the latest news, tips and updates.